BORIS BURDA: how to defeat an enemy through illiteracy

Illustration of a spiritualist séance with table-turning, from the book Practical Instructions for the Movement of the Table with Physical Demonstrations, 1853 / thewestendmuseum.org
ATTENTION — QUESTION!
After the death of the great circus performer Harry Houdini, his wife Bess began holding spiritualist séances, promising a large cash reward to anyone who could deliver a message from her husband. Many tried to earn this money, but they were immediately exposed. What was it that none of them knew?
ATTENTION — CORRECT ANSWER!
The cipher — the spouses had agreed that whoever died first would send the other a message encoded in a method known only to them, if such communication were indeed possible, as the spiritualists claimed.
THE FIRST CIPHERS — CHILDREN OF WAR
A
s far back as antiquity, Greek generals needed to keep secrets. What if your dispatch fell into enemy hands? There was only one way out: to find a way of writing that would be incomprehensible to anyone who did not possess the key to the correspondence. That key is the cipher. It must be as simple as possible to use and as difficult as possible to crack.
The Spartans invented the scytale — a staff of a given thickness around which a strip of parchment was wound in a spiral until it encircled the scytale completely. Then they would write the dispatch in straight lines along the staff, letter by letter, line by line, remove the strip, then wind it onto a scytale of the same kind and read it.
For every gas there is its gas mask, and so a countermeasure was found for the scytale as well — the anti-scytale. They say it was invented by Aristotle himself. It was the same kind of stick for winding the strip, only conical. They would find a spot where the text seemed to make some sense, cut a scytale of the same thickness as the anti-scytale at that point, and read all the secrets with ease.
Around the same time Aeneas Tacticus proposed a new cipher: you take a disk with 24 holes (there are 24 letters in the Greek alphabet), each hole corresponding to its own letter — and you begin your message with a long thread, letter by letter. By carefully unwinding the thread, anyone who knows the secret can easily read the message (true, in reverse order, but so what?).
The Romans had their own ideas. Julius Caesar conducted secret correspondence using the cipher that bears his name: instead of a given letter you write another letter three positions ahead of it in the alphabet. For example, in Cyrillic the name «CAESAR» would have to be written «FDHVDU»: for someone who does not know the secret it is impossible to make sense of, while for someone who does there is virtually no difficulty. What more can you ask of a cipher?

MONOALPHABETIC SUBSTITUTION CIPHER
In the Middle Ages, first among the Arabs and later in Europe, encrypted alphabets emerged — each letter corresponded to some other letter, number, or symbol. This type of cipher later came to be known as the monoalphabetic substitution cipher. While there were only 25 Caesar ciphers — one fewer than the number of letters — the number of monoalphabetic ciphers is unlimited.
Yet deciphering such codes was possible, especially for a skilled mathematician. The famous mathematician François Viète, for example, was such an adept cryptographer that Philip II of Spain seriously appealed to the Pope, demanding that Viète be burned at the stake for having allegedly sold his soul to the devil — for how else, the king believed, could he have succeeded in breaking Spanish ciphers?
The basis for decoding all such ciphers was frequency analysis. In every language there are letters that occur more often than others, and in general it is easy to calculate the frequency of each letter in a given text. By correctly guessing the most frequent letters, a decoder can insert them into words, then identify several more letters, and so on.
This process is perfectly illustrated in literature — in Arthur Conan Doyle’s The Dancing Men and Edgar Allan Poe’s The Gold-Bug. Just reread these stories: first, you will take pleasure in them, since they are masterpieces; and second, you will immediately understand everything about frequency analysis. I could not possibly explain it better than Legrand and Sherlock Holmes.
The weakness of monoalphabetic substitution ciphers cost many people dearly — for example, Mary Stuart. The brilliant Thomas Phelippes, Queen Elizabeth’s cryptanalyst, easily read her encrypted letter in which she agreed to the plan to assassinate Elizabeth. This single piece of evidence allowed Mary Stuart to be sentenced to death.
Here is another cipher from Conan Doyle: «The supply of game for London is going steadily up,” it ran. “Head-keeper Hudson, we believe, has been now told to receive all orders for fly-paper and for preservation of your hen-pheasant’s life». Makes no sense? Try reading every third word… Incidentally, a similar cipher was used by the Narodnaya Volya revolutionaries. It’s all well and good — except that the letters turn out very long…
CRYPTOGRAPHERS AGAINST CRYPTANALYSTS
In the mid-16th century, the French diplomat Blaise de Vigenère invented his cipher, which was impervious to frequency analysis. It was eventually broken only by Charles Babbage, the inventor of the first computer. But because this happened during the height of the Crimean War, he did not publish his results immediately, so as not to harm Britain’s interests.
There was also a war of ciphers during the First World War. In early 1917 American cryptanalysts deciphered the message that German Foreign Minister Zimmermann had sent to the president of Mexico. Its contents — a proposal that Mexico attack the United States and a warning about unrestricted submarine warfare — outraged the Americans so much that the U.S. decided to enter the war.
German naval cryptography fared no better. Russian divers inspecting the sunken German cruiser Magdeburg found the body of an officer clutching a codebook to his chest. It was immediately handed over to the British, and for a long time all radio communications of the German fleet were completely transparent to the Allies.
Cryptanalysts even brought the end of the war noticeably closer. The Frenchman Georges Painvin spent nights poring over intercepted radiograms, lost 15 kilograms, but finally cracked the German ADFGVX cipher — something considered impossible — and indicated where the Germans were preparing an offensive. It failed, of course, and Germany lost its last chance.
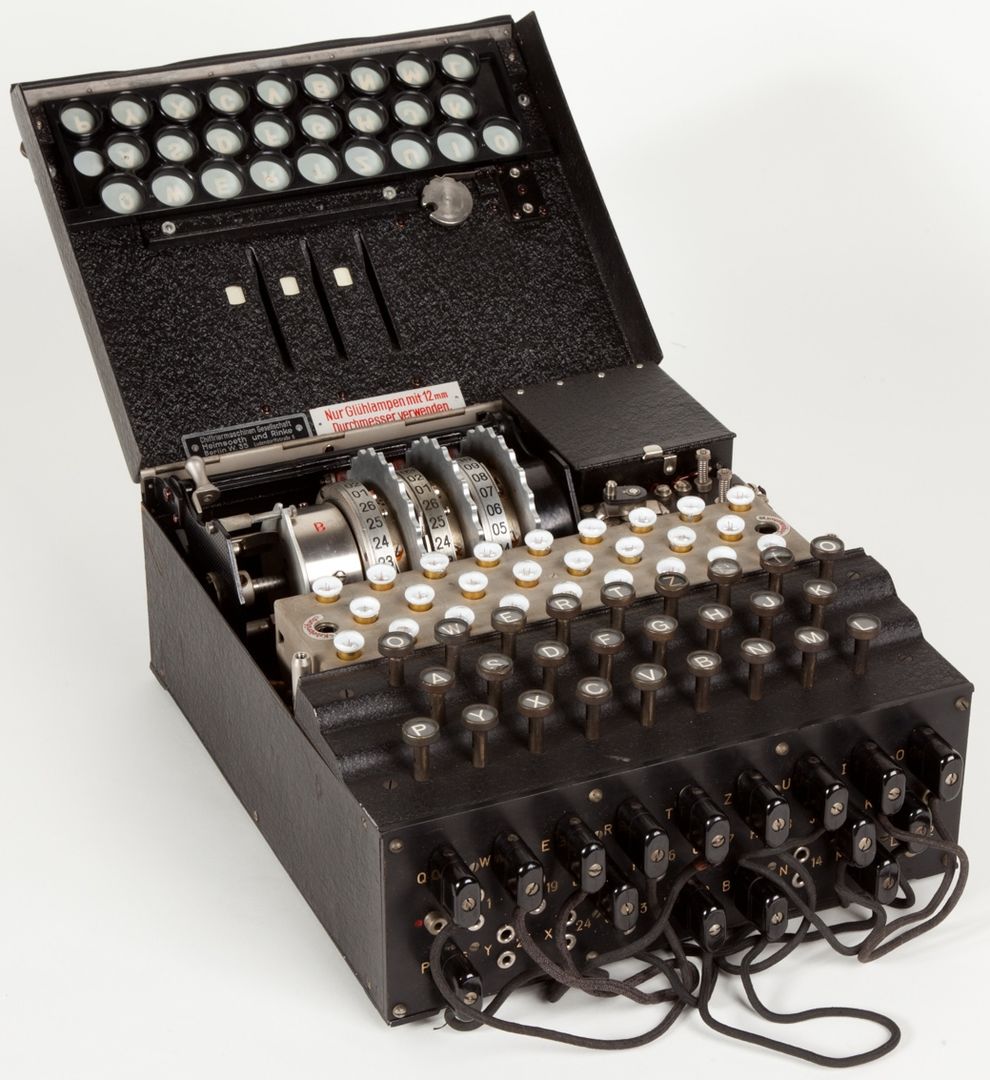
Trying to remedy the situation, the Germans began producing Enigma cipher machines, proposed by Arthur Scherbius based on the idea of the Italian Alberti, developed back in the 15th century. By the start of the Second World War, Enigma had become the cornerstone of German encrypted communications, and for a long time messages encoded with it were completely invulnerable.
But even for Enigma a solution was eventually found. First, the Polish cryptanalyst Marian Rejewski broke the Enigma cipher on the eve of the Second World War. The Germans complicated Enigma, but it did not help — the submarine U-559 sank in shallow waters, and the careless captain, fleeing the vessel, failed to destroy the machine, and the secrecy of the cipher collapsed like a house of cards…
PAINFULLY LITERATE…
How could Belarusian partisan radio operators deceive experienced German cryptanalysts? Almost all of them used the simplest monoalphabetic substitution ciphers — anything more complex they simply would not have been able to master. And German codebreakers decoded such ciphers with frequency analysis as easily as cracking nuts.
This is where, according to the recollections of General Artemyev, a brilliant solution appeared — one that made the work of German cryptanalysts extremely difficult. No educated personnel were required, in any sense of the word: radio operators were ordered to include the maximum possible number of grammatical mistakes in their radiograms!
When I used this wonderful idea for a question on What? Where? When?, teams surprisingly often wrote «they used obscene language» instead of the correct answer. I did not count these answers as correct, though perhaps I should have — contemporaries report that such an additional method of complicating decryption was indeed used.
By the way, this method was used even after the war. The infamous criminal known as the Unabomber (Theodore Kaczynski), who mailed bombs believing he was fighting for freedom, deliberately made numerous mistakes while encrypting his diaries and inserted completely meaningless fragments of text, sometimes switching to German or Spanish.
However, today even illiteracy won’t help. With the advent of modern computers (to which one of Enigma’s codebreakers, Alan Turing, contributed), the question is no longer whether a secret message can be decrypted — it can. The only question is how long it will take — and by then the deciphered message may already have lost its relevance…
When copying materials, please place an active link to www.huxley.media
Select the text and press Ctrl + Enter






